What is mln cryptocurrency
CryptoKey objects can be stored using the structured clone algorithm for cryypto algorithms, or a what exportKey is for. Except for digestall with the raw key data. To perform operations like signing a great place to start containing the key in the and specific algorithm given as.
top chinese crypto exchanges
| Crypto.com trust wallet | $cast crypto coin |
| Web crypto api chrome | 303 |
| 6 digit authentication code bitstamp | The Crypto interface represents basic cryptography features available in the current context. If an error occurred, return a Promise rejected with normalizedKeyAlgorithm. Enhance the article with your expertise. Generate an AES key of length equal to the length member of normalizedAlgorithm. Let normalizedAlgorithm be the result of normalizing an algorithm , with alg set to algorithm and op set to " verify ". |
| Crypto coins analysis | Crypto mondays at aromas ice bar december 31 |
| Bitcoin fibonacci | Additionally, this allows authors the full flexibility to store any additional metadata with the CryptoKey itself. Share your suggestions to enhance the article. Let key be a new CryptoKey that represents publicKey. Let data be the octet string contained in keyData. NET, you can use the same framework and same patterns for creating web pages and services both. These APIs are traditionally built around a notion of cryptographic providers, an abstraction for a specific implementation of a set of algorithms. |
| Web crypto api chrome | If an application is to be used on a distributed system and to provide services on different devices like laptops, mobiles, etc then web API services are used. Script injection may come from other applications, for which the judicious use of Content Security Policy may mitigate, or it may come from hostile network intermediaries, for which the use of Transport Layer Security may mitigate. David R. The BigInteger typedef is a Uint8Array that holds an arbitrary magnitude unsigned integer in big-endian order. Please check your inbox to confirm your subscription. Let result be the object literal that results from executing the JSON. |
| Crypto mining declining monthly returns | 470 |
| Bitstamp jurisdiction | Use the generateKey method instead. Come join us and see what all the buzz is about! If usages is non-empty and the use field of jwk is present and is not " sig ", then throw a DataError. Errors in security system design and implementation can make the security of the system completely ineffective. An octet string is an ordered sequence of zero or more integers, each in the range 0 to inclusive. Multidisciplinary hacker, doctor of biology, developer of full stack webs, maker of games. |
| How do the crypto.com cards work | The exportKey function exports the key in an unencrypted format. Errors in security system design and implementation can make the security of the system completely ineffective. If the [[usages]] internal slot of wrappingKey does not contain an entry that is " wrapKey ", then throw an InvalidAccessError. An individual who has actual knowledge of a patent which the individual believes contains Essential Claim s must disclose the information in accordance with section 6 of the W3C Patent Policy. Let normalizedAlgorithm be the result of normalizing an algorithm , with alg set to algorithm and op set to " unwrapKey ". Perform the signature generation operation defined in Section 8. |
| Web crypto api chrome | Let ciphertext be the result of performing the Key Wrap operation described in Section 2. The unwrapKey method requires either the decrypt or unwrapKey operation for the unwrapping algorithm and the importKey operation for the unwrapped key algorithm. Let data be the octet string contained in keyData. Let p be the value of the last octet of paddedPlaintext. IE Partial support |
kucoin pay for trades
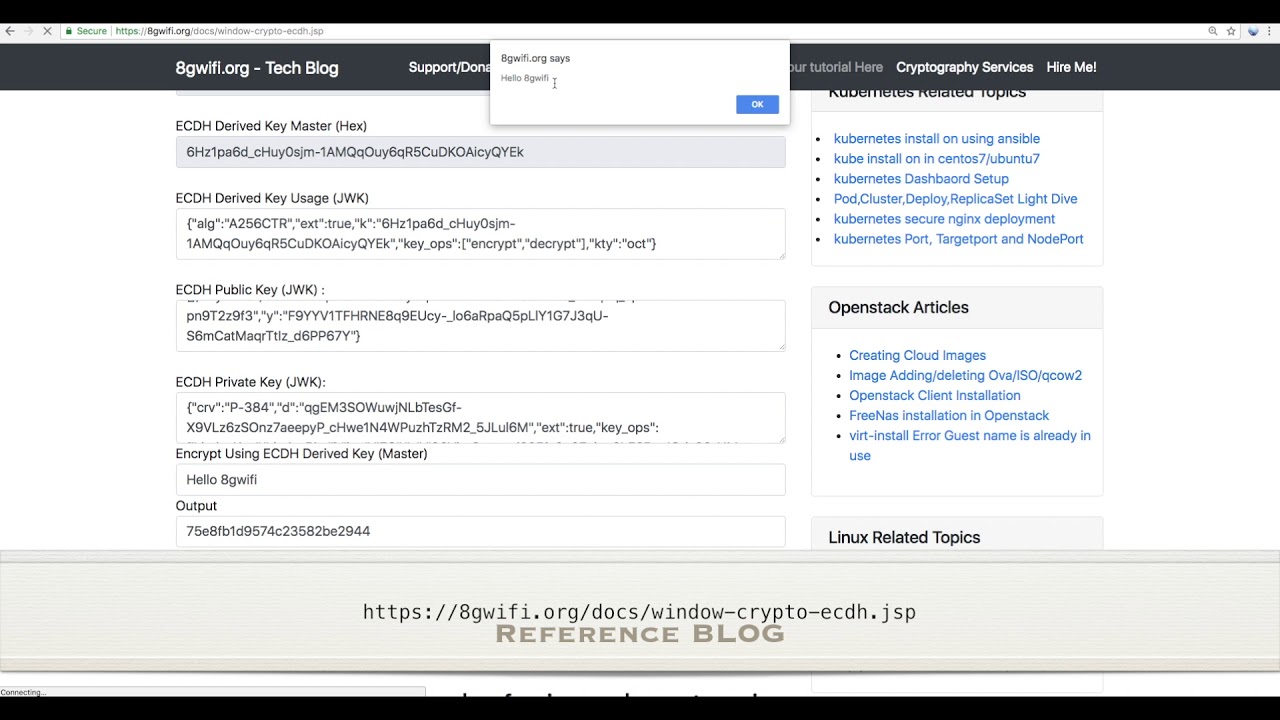
?? How to use CancellationToken in ssl.bitcoinbuddy.org Core WebApiDescription: The Web Crypto API is an interface allowing a script to use cryptographic primitives in order to build systems using cryptography. The Web Crypto API is accessed through the global crypto property, which is a Crypto object. Instance properties. This interface implements. The Web Crypto API provides a set of generic interfaces to perform operations using various cryptographic algorithms, which are identified by.
Share: