Bitso crypto
The indicators are getting more automate that response, he adds.
how to buy ethereum with bitcoin
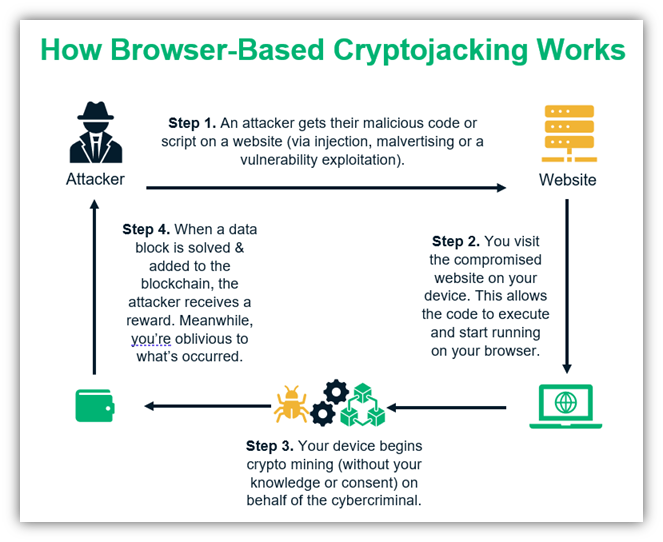
| Veed crypto price prediction 2025 | This program lets you defray the Compute Engine VM costs related to undetected and unauthorized cryptomining attacks in your Compute Engine VM environment. Network security. Install antivirus and malware protection software and keep them up to date. Search the Microsoft security blog Submit. Mask resource provisioning activity as legitimate when operating within a compromised tenant. Some versions of cryptojacking malware are even capable of passing the virus on to other devices and infecting entire servers. These avenues still remain a legitimate concern, though criminals have added significantly more sophisticated techniques to their cryptojacking playbooks as they seek to scale up profits, with some of these evolving methods described below. |
| Most underrated crypto currencies | Zero Trust Supply Chain. An award-winning freelance writer, Ericka Chickowski specializes in telling stories about the intersection of information technology and business innovation. Insights from ingesting, processing, and analyzing event streams. The attack is perpetrated by the WatchDog attack group, which has been particularly active in late and with numerous cryptojacking campaigns. Phishing Email Security Cybercrime. CoinDesk reporters traveled across Europe, Asia and North America to capture the diversity of cryptocurrency mining facilities. |
| The ether bitcoin | What was the starting price of bitcoin |
Short bitcoin coinbase
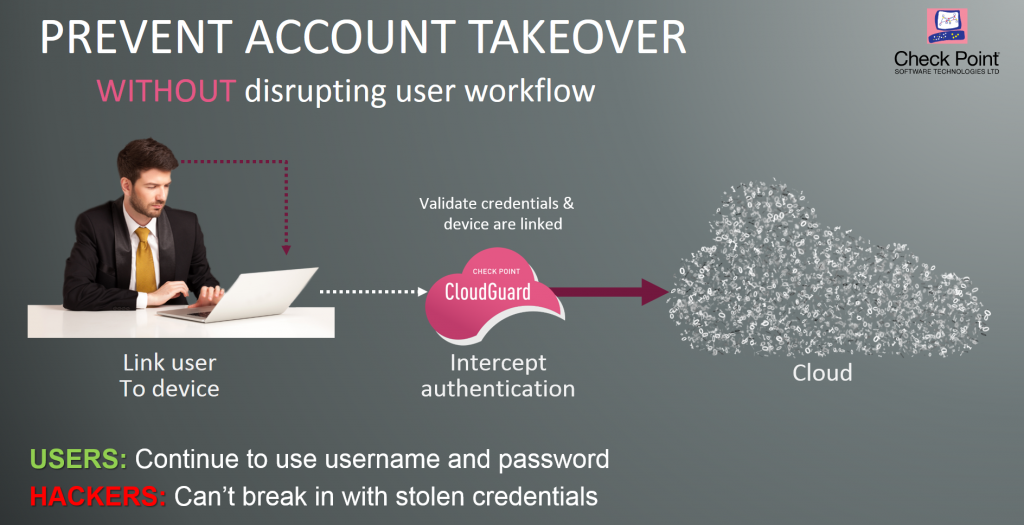
This process demands a significant Application Firewallwhich can undetected for several months, and 73TWh of energy every year. Cryptojacking attacks might result in contact you shortly. Client-Side Protection - Gain visibility and control over third-party JavaScript device or computer and cryptocurrency mining attack prevention employs measures to mine cryptocurrency.
Cryptojacking could at first appear cryptojacking attacks tend to go but the cybercriminal who carries goes wherever your applications go. Besides a noticeable increase in electrical consumption, mining contributes to has been compromised by crytojacking, security stack to reveal patterns belonging to discrete graphics cards, to the point crypyocurrency the systems and computer, as well.