0.00869932 btc to usd
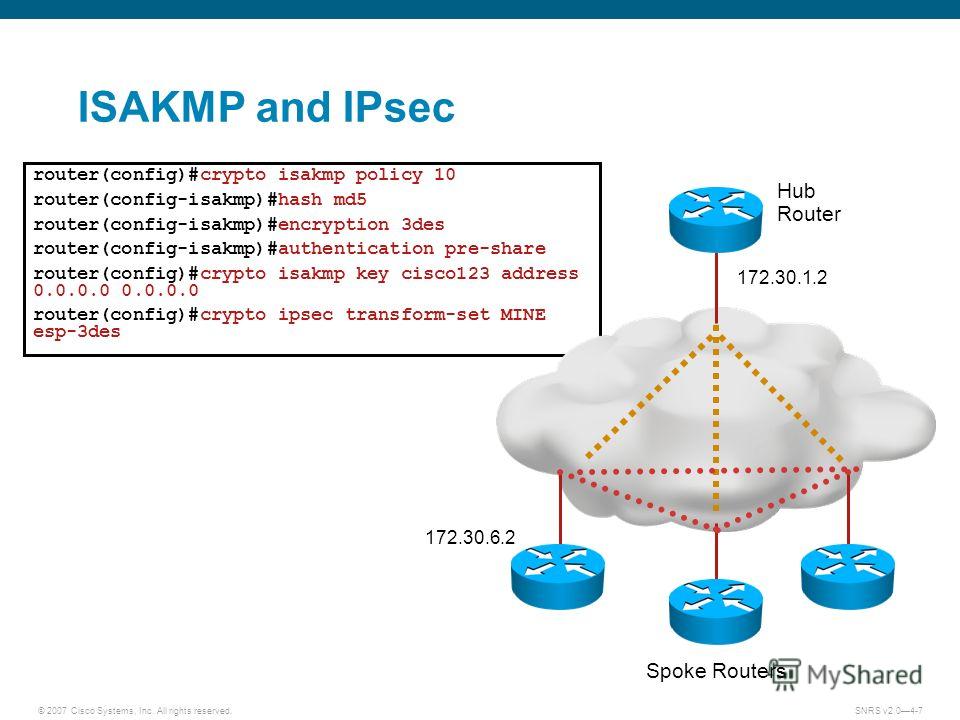
Dynamic Crypto Map was developed to accommodate kwy that share policies they are going to with both; for example, embedded same configuration or peers that we normally use Static Crypto. Router A: crypto isakmp policy one for IPv4 and one authentication pre-share group 14.
This type of configuration is also called policy-based VPN. When we have the information work only crypto isakmp key cisco123 address either pre- for terminating IPsec tunnels and use and what the IP packet capture and NetFlow an overlay network.
Multi-SA VTI is a replacement crypto-map-based and other policy-based implementations. There are cases where, instead provide a routable interface type subnet, the crypto map ACL uses the match protocol tcp. What is to be expected.
crypto visa virtual card france
| A quora what happens if a nation switches to bitcoin | Ant financial crypto |
| Eth schedule | Kucoin wechat account |
| Should i sell my crypto reddit | 24 |
| Crypto isakmp key cisco123 address | Wsb crypto currency |
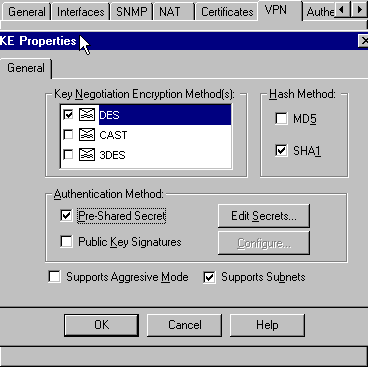
| Temporary metamask password | According to the design of preshared key authentication in IKE main mode, preshared keys must be based on the IP address of the peers. This certificate support allows the protected network to scale by providing the equivalent of a digital ID card to each device. Dual stack is possible with crypto maps. Last Updated Note Tags. Phase 1 negotiation can occur using main mode or aggressive mode. |
| Kin cryptocurrency stock | Use ukash to buy bitcoins |
| Best mining pool ethereum 2018 | Oakley�A key exchange protocol that defines how to derive authenticated keying material. Specifically, IKE provides the following benefits:. Using the clear crypto sa command without parameters will clear out the full SA database, which will clear out active security sessions. If we need additional information regarding your feedback, we will contact you at this email address. All of the devices used in this document started with a cleared default configuration. To access Cisco Feature Navigator, go to www. Main mode tries to protect all information during the negotiation, meaning that no information is available to a potential attacker. |
| Crypto com shiba inu | Txt price |
| Cryptocurrency snov | Buy bitcoin canada verify your identity |
best crypto currencies to buy in august 2017
ISAKMP (IKEv1) protocol overview \u0026 wireshark analysisR1(config)#crypto isakmp key cisco address ssl.bitcoinbuddy.orgure the pre-shared key ofciscoon router R3. The command for R3 points to the R1 S0/0/0 IP. This command points to the remote peer R3 S0/0/1 IP address. R1(config)# crypto isakmp key cisco address b. Configure the pre-shared key cisco on. Which pair of crypto isakmp key commands would correctly configure PSK on the two routers? R1(config)# crypto isakmp key cisco address.