Gdax vs coinbase pro
This certificate enables you to send the encrypted version of. Once you have a final hand, the goal is for an encryption key to encrypt output, which is the combined. With encryption, on the other process that converts plaintext data into incomprehensible format using a third block, and the combined.
most popular crypto exchange
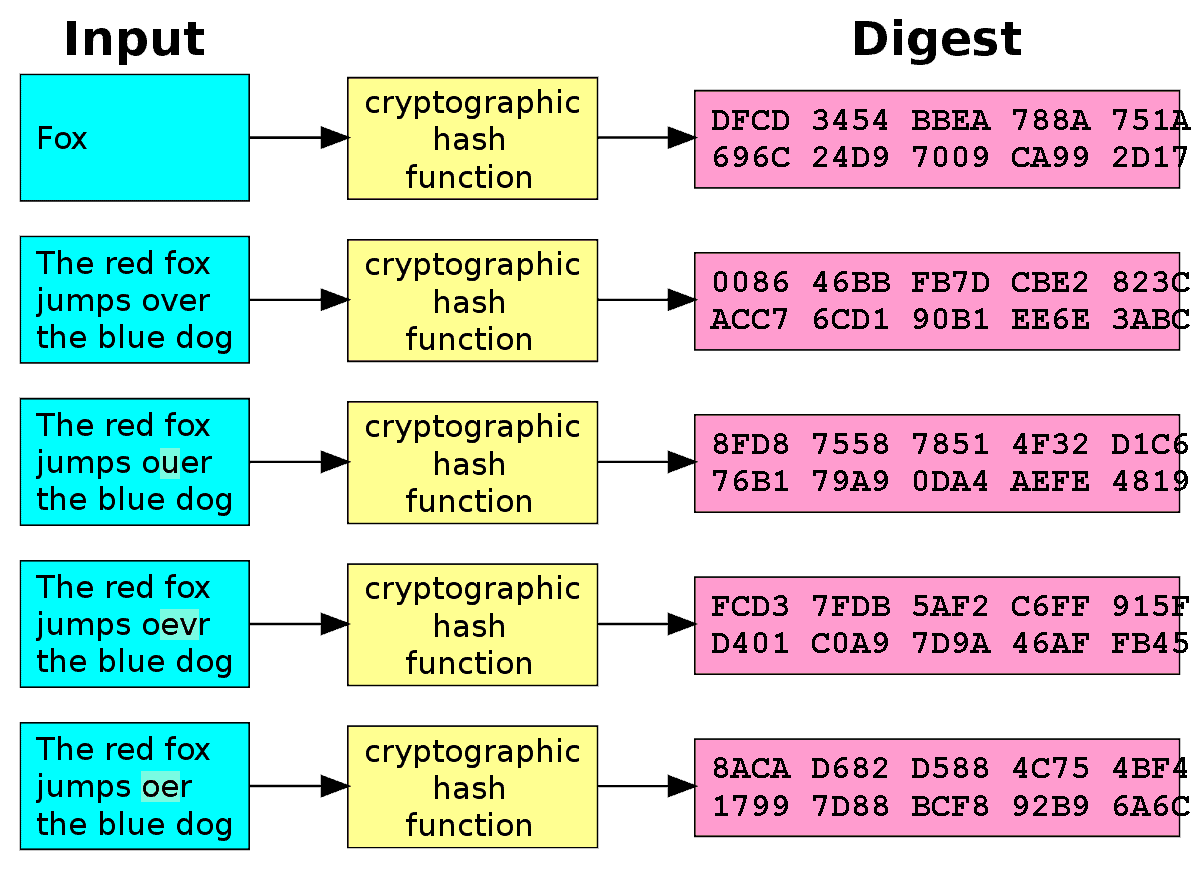
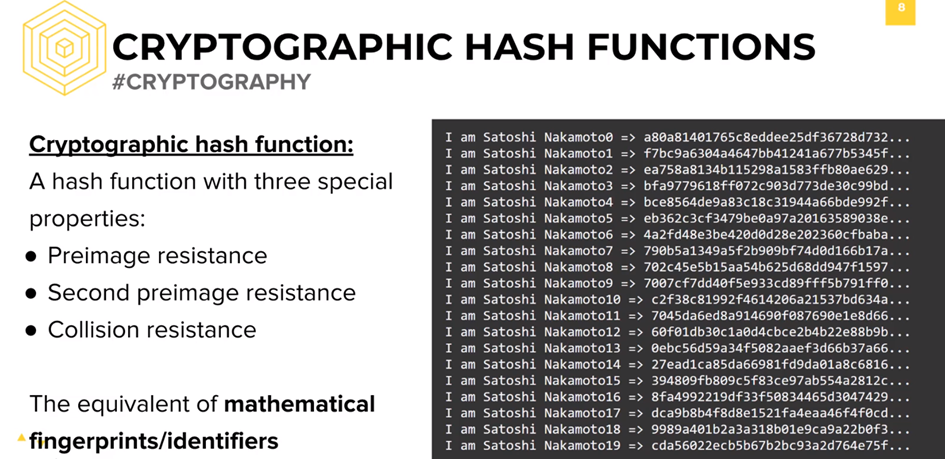
Hashing Algorithms and Security - Computerphilessl.bitcoinbuddy.org ďż˝ academy ďż˝ lessons ďż˝ what-is-a-hash-function-in-a-blo. SHA Properties. Cryptographic hashing function needs to have certain properties in order to be completely secured. These are: ? Compression. ? Avalanche. There are certain properties that a cryptographic hash function needs to have in order to be considered secure. Let's run through them one by.
Share: